Infrastructure Penetration Testing
Infrastructure Penetration Testing
Infrastructure Penetration Testing focuses on servers, workstations, firewalls, routers, and internal/external networks. Students learn how attackers move inside networks, exploit weak services, misconfigurations, and unpatched systems.
For companies, our testing provides actionable insights to strengthen network defenses. For students, these projects simulate real SOC and red-team environments, preparing them for infrastructure security, SOC analyst, and pentester roles.
Penetration Testing Methodology Summary
Mapping and Enumeration
The initial steps of the engagement include determining the attack surface for all in-scope systems, including host discovery, port scanning, service version scanning, and domain enumeration.
Vulnerability Identification and Confirmation
This stage includes the manual work performed by the tester to highlight security vulnerabilities; where authorised it will include the active exploitation of vulnerabilities to ensure that risks are appropriately graded, and false positives are removed. This includes service testing for issues such as known vulnerabilities, common and default misconfigurations, as well as manual testing for insecure services. It will also include testing of authentication systems, such as testing for weak passwords, default credentials, and insufficient account lockout policies.
Finally, network traffic will be assessed for weaknesses in-transit protection such insufficient cryptographic protection and insufficient protection against interception and relay attacks.
Privilege Escalation and Propagation
Privilege Escalation typically includes two main stages: escalation from domain user to local administrator, and escalation from local administrator to domain administrator. Where possible network propagation will be assessed to determine issues, such as reused administrative credentials.
This stage includes assessing local services for weaknesses such as insecure services paths and permissions, as well as testing for credentials in plaintext, token impersonation, and administrative session interception.
Post Exploitation
Once a compromise is achieved additional attack vectors are assessed, credential audits are performed, and risk assessments are performed to determine what level of system access could be achieved and the level of skill required by the attacker to perform the exploitation.
Remediation
We don’t just focus on vulnerability discovery, but we also give significant detail on remediating discovered vulnerabilities and importantly, hardening systems against exploitation.
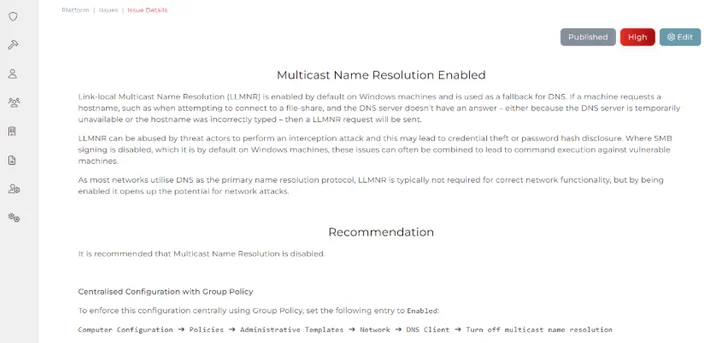
We don’t just focus on vulnerability discovery, but we also give significant detail on remediating discovered issues and importantly, hardening systems against exploitation. During the engagement you can track the findings within our web platform, allowing you to follow how the test is progressing but also to get a head start on remediating discovered issues. Once the assessment is complete, we will deliver a detailed report of findings and remediation guidance, as a record of your assessment.
During the engagement you can track the findings within our web platform, allowing you to follow how the test is progressing but also to get a head start on remediating discovered issues. Once the assessment is complete, we will deliver a detailed report of findings and remediation guidance, as a record of your assessment.
We don’t just focus on vulnerability discovery, but we also give significant detail on remediating discovered issues and importantly, hardening systems against exploitation.

Need 24/7 Protection From Cyber Attacks?
We Find Vulneraabilities Before They Are Exploited
We Train You on Real Tools & Scenarios
We Make You Job-Ready
Get in Touch With </Hacker4Help>